Exploring Transposition Ciphers
Introduction
This section only includes the two examples of transposition ciphers. Both are based on switching the position of letters according to an algorithm. There are lots of minor and major variations that can be introduced to these processes that make them more secure.
There are more transposition ciphers that have been used, some of those are mentioned on this page in case you feel like working out your own implementation of them.
Rail Fence Variations
Classical rail fence involved writing the message oout in a zigzag fashion according to a predetermined number of rails - the key to the message.
| T | - | - | - | E | - | - | - | T | - | - | - | U | - |
| - | H | - | S | - | C | - | E | - | I | - | O | - | T |
| - | - | E | - | - | - | R | - | - | - | S | - | - | - |
There are other ways you might choose to do this. The simpler method that is more often used would write the message out like so,
| T | - | - | S | - | - | R | - | - | I | - | - | U | - |
| - | H | - | - | E | - | - | E | - | - | S | - | - | T |
| - | - | E | - | - | C | - | - | T | - | - | O | - | - |
Another way to lay out the message might be to alternately take letters from the beginning and end of the message as the rails are constructed. This further disturbs the order of the letters.
Columnar Transposition Variations
In our example on the page, we padded out the grid with a random character to make sure that all spaces were filled. There is no real need to do this, although knowing that the grid is regular makes the programming easier. We could have just used the grid as it is,
| L | E | M | O | N |
|---|---|---|---|---|
| T | H | E | S | E |
| C | R | E | T | I |
| S | O | U | T | R |
| U | N | A | N | D |
| H | I | D | E |
Myszkowski Transposition
This named variant dates to the turn of the 20th century. It is an adjustment to the way that the keyword is used to order columns. Assume that we have the keyword, 'SECRET'. It has a repeated letter in there. With columnar transposition we either reject this key or make the order of columns as follows,
| 4 | 1 | 0 | 3 | 2 | 5 |
|---|---|---|---|---|---|
| S | E | C | R | E | T |
With Myszkowski transposition, you use the same index for repeated letters,
| 3 | 1 | 0 | 2 | 3 | 4 |
|---|---|---|---|---|---|
| S | E | C | R | E | T |
When it comes to forming the cipher text, the repeated columns are written out left-to-right, the other ones as normal. With our original message and this new numbering system,
| S 3 | E 1 | C 0 | R 2 | E 1 | T 4 |
|---|---|---|---|---|---|
| T | H | E | S | E | C |
| R | E | T | I | S | O |
| U | T | R | U | N | A |
| N | D | H | I | D | E |
ETRH HEES TNDD SIUI TRUN COAE
Disrupted Transposition
Another way to vary the impact of columnar transposition is to place gaps or random characters within the grid. A single random letter in the middle of a word would not trouble anyone who decrytped the message using legitimately. It would make it more difficult to use 'anagramming' to guess the column order. There are two possibilities here,
Spaces: You could introduce some spaces at predefined positions in the plain text message. There could be left in the message when the columns are formed. The positioning of spaces in the cipher text is normally regular (or they are removed). One approach might be to use a known sequence to determine the position of the spaces. The number Π (PI) is quite a useful one here. The decimal places of the number start 14159 and continue with no discernible pattern. Using this sequence, we could adjust the plain text as follows,
- Take 1 character from the plain text, add a space
- Take 4 characters from the plain text, add a space
- Take 1 character from the plain text, add a space
- Take 5 characters from the plain text, add a space
- Until there are no more characters left in the plain text
Random Characters: The second approach is to add letters in random positions. If a lot of letters are added, a key might be needed. If there aren't too many, the message is likely to remain readable when decrypted. There is a balance to be struck here. Working out the frequency of your replacements is the key to the method.
Other Ways To Transpose
Route Cipher
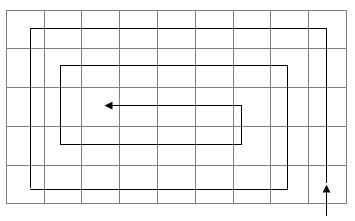
Messages are written out on a grid. The key to deciphering the message is to know the order in which the letters are supposed to be read. This is the 'route' for the cipher. An example of a route might be a spiral like this,
Grilles
A grille is the name given to a pattern of holes that you lay over a grid. The holes expose some letters and obscure others. Take the following grid of letters,
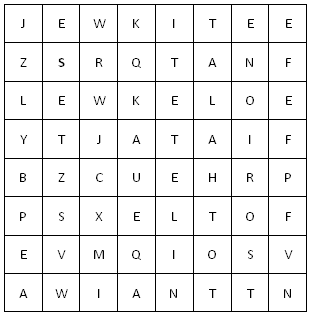
Place a grille over the top of the grid to reveal the 'secret' message,
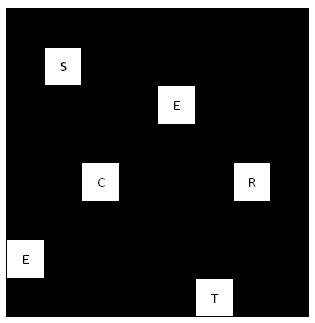
Even more ingenious is a 'turning grille'. The grille is made so that, when rotated, it exposes different letters in the grid.

